Setting Up a G Network for Cloud Security: A Comprehensive Guide
As the adoption of cloud computing continues to grow, organizations are becoming increasingly dependent on cloud-based services to store and process sensitive data. However, this shift to the cloud has also introduced new security concerns. One of the most critical aspects of cloud security is the network, which acts as the backbone of your cloud infrastructure. In this article, we'll explore the process of setting up a G network for cloud security, a crucial step in protecting your organization's data.
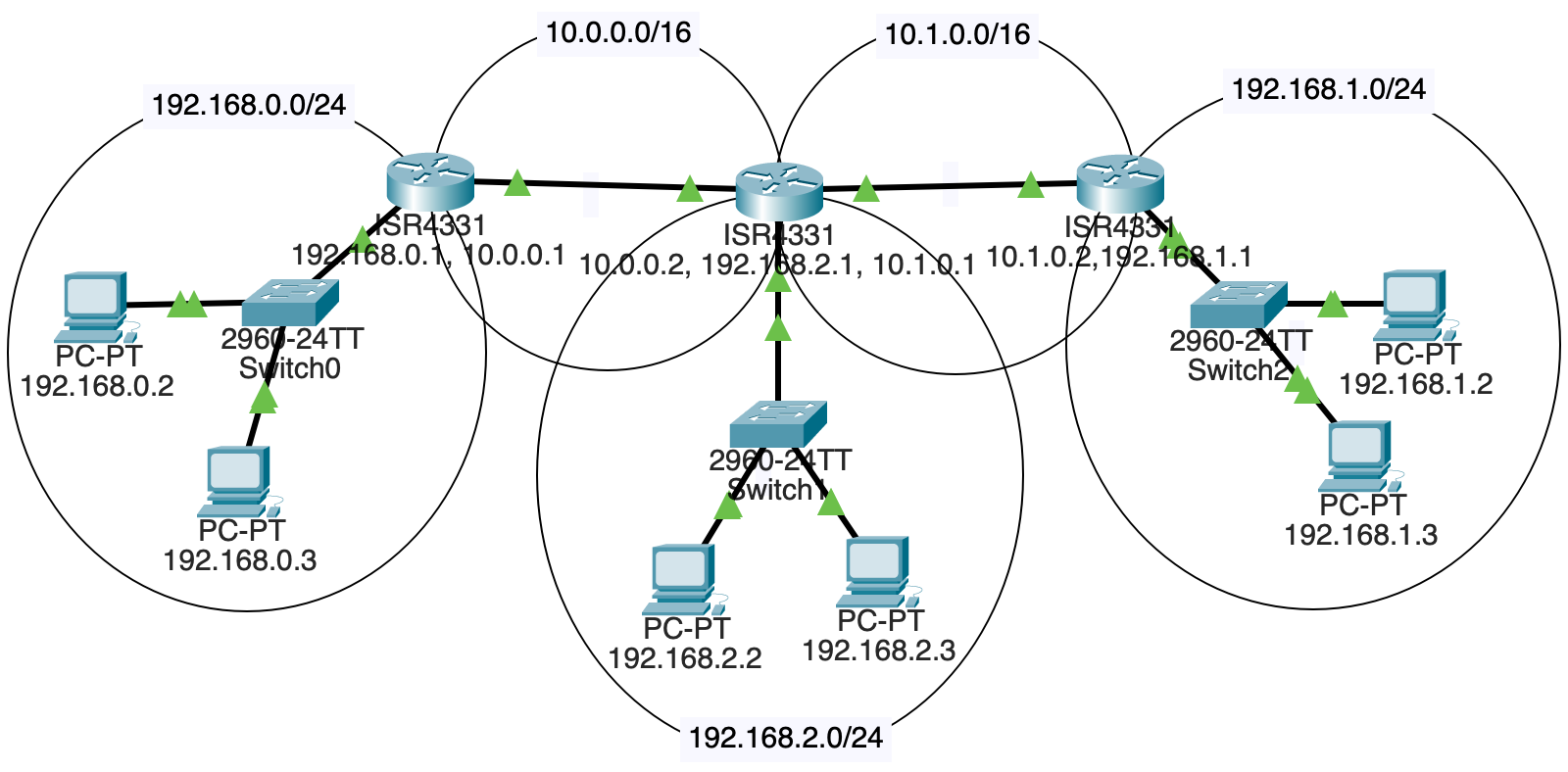
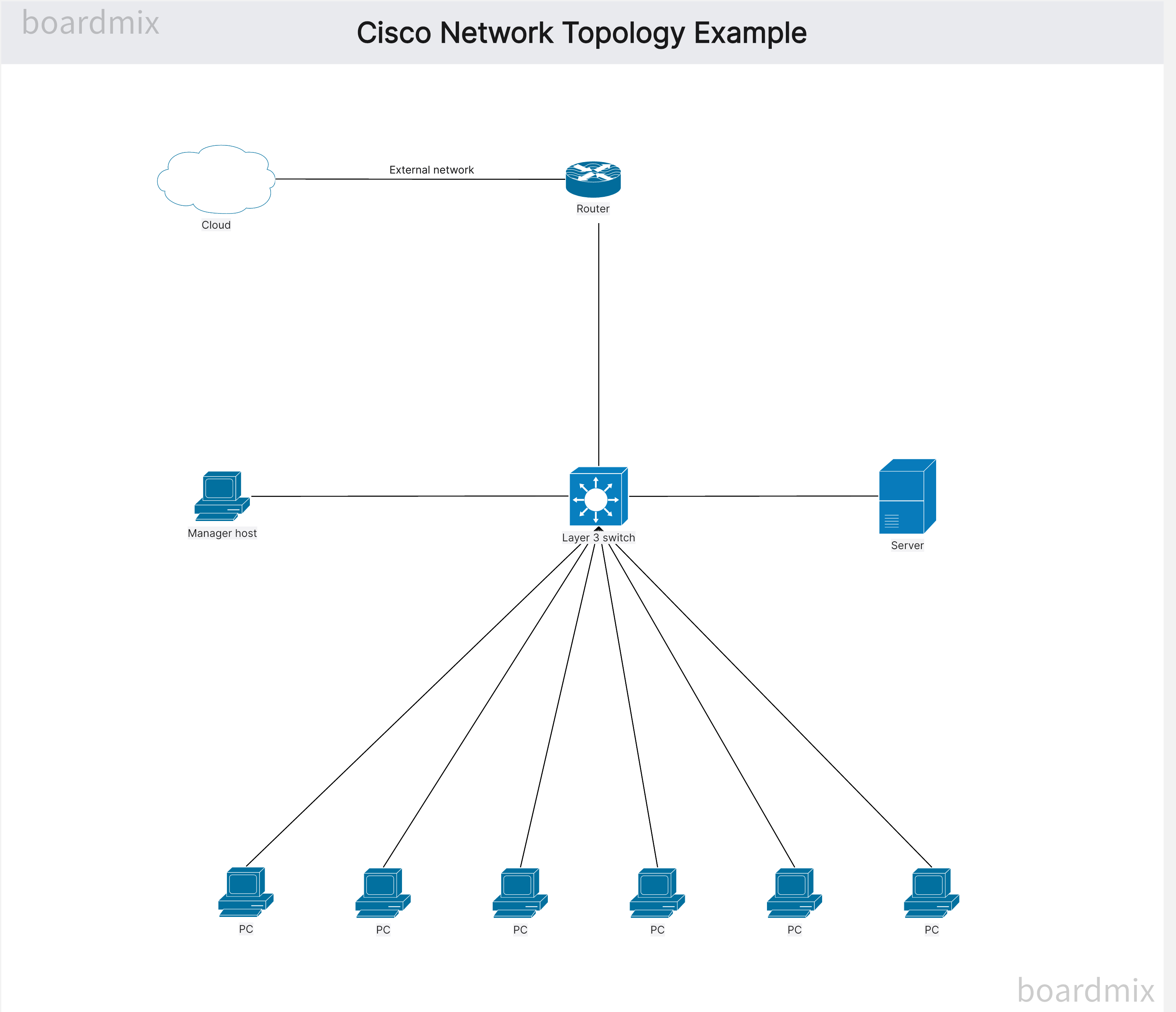
Google Cloud Network (GCN) is a networking service provided by Google Cloud that allows users to create a virtual private cloud (VPC) infrastructure. With GCN, you can create multiple virtual networks, subnets, and firewall rules to secure your cloud resources. A well-designed GCN is essential for ensuring the security and scalability of your cloud applications.
Setting Up a G Network for Cloud Security: Key Components

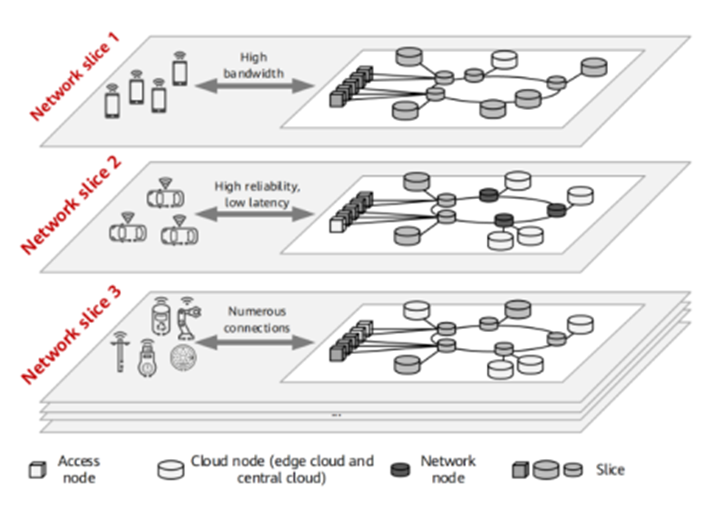
Furthermore, visual representations like the one above help us fully grasp the concept of Setting Up A G Network For Cloud Security.
Setting up a G network for cloud security involves several key components:
- Virtual Private Cloud (VPC): A VPC is a virtual network infrastructure that provides a secure and isolated environment for your cloud resources. You can configure VPCs to meet your specific needs, including choosing the subnet size, IP range, and firewalls.
- Subnets**: Subnets are smaller networks that are part of a larger VPC. They help to organize your cloud resources and ensure that they're properly isolated.
- Firewall Rules**: Firewall rules determine which traffic is allowed in and out of your VPC. You can configure rules to block or allow specific types of traffic, ensuring the security of your cloud resources.
- Google Cloud Network Interfaces (VCNs)**: VCNs are virtual interfaces that connect your cloud resources to your VPC. You can configure VCNs to provide additional security features, such as encryption and access controls.
While setting up a G network for cloud security involves several key components, there are several best practices you should follow to ensure the security and scalability of your cloud resources:

- Implement Segmentation**: Segmentation involves dividing your network into isolated segments to prevent lateral movement of attackers. This helps to contain potential security breaches and prevent the spread of malware.
- Use Secure Internet Gateways (SIGs)**: SIGs provide an additional layer of security by inspecting internet traffic and blocking malicious traffic before it reaches your VPC.
- Apply Security Controls**: Apply security controls, such as firewalls and access controls, to ensure that only authorized users and systems have access to your cloud resources.
- Regularly Monitor and Audit**: Regularly monitor and audit your G network to detect potential security breaches and identify areas for improvement.
Conclusion
Setting up a G network for cloud security is a critical step in protecting your organization's data and ensuring the security and scalability of your cloud applications. By understanding the key components of a G network and following best practices, you can create a secure and isolated environment for your cloud resources. Remember, security is an ongoing process that requires regular monitoring and auditing to ensure the integrity of your cloud infrastructure.