Online Credit Card Users Tracking Protocol: A Comprehensive Guide
Introduction
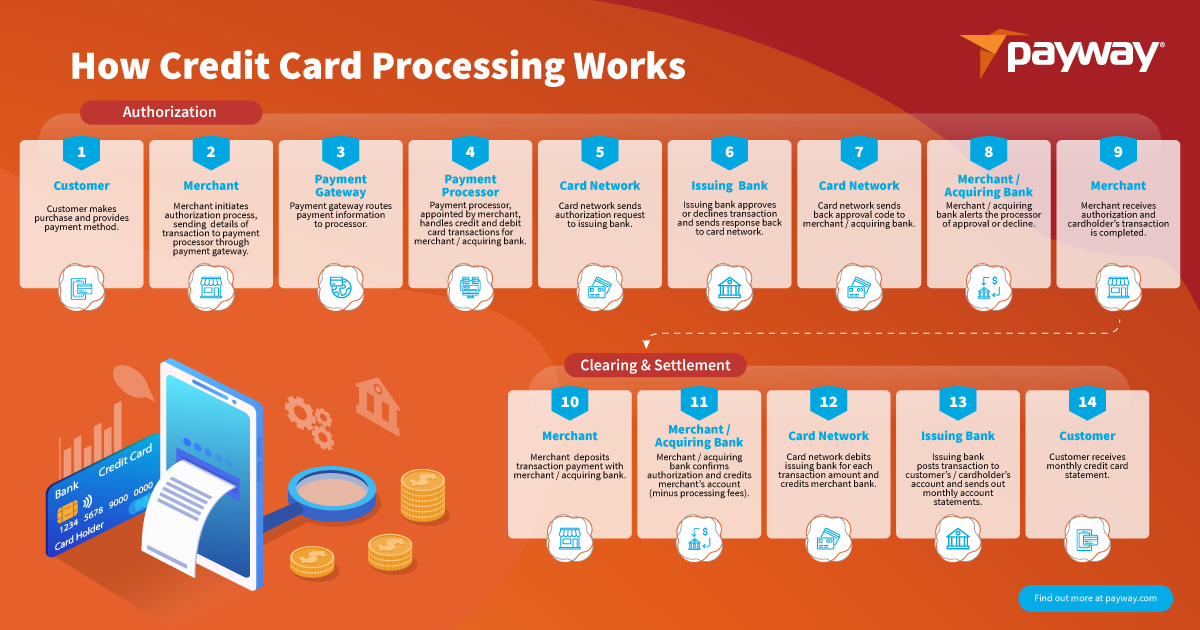
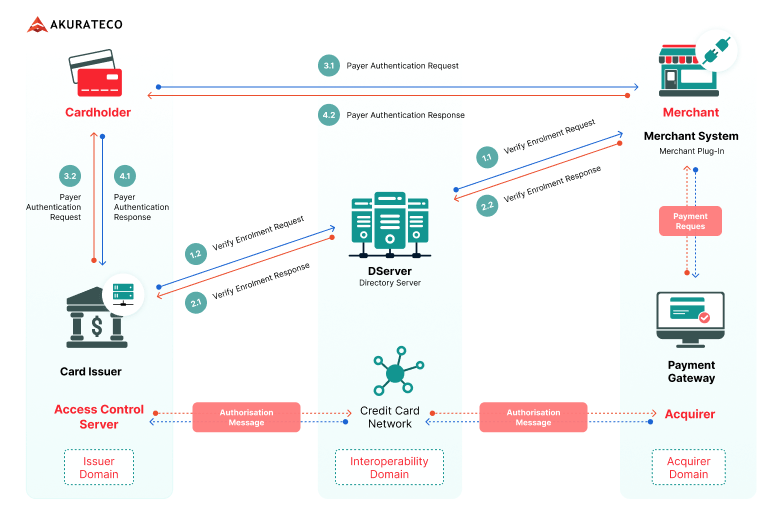
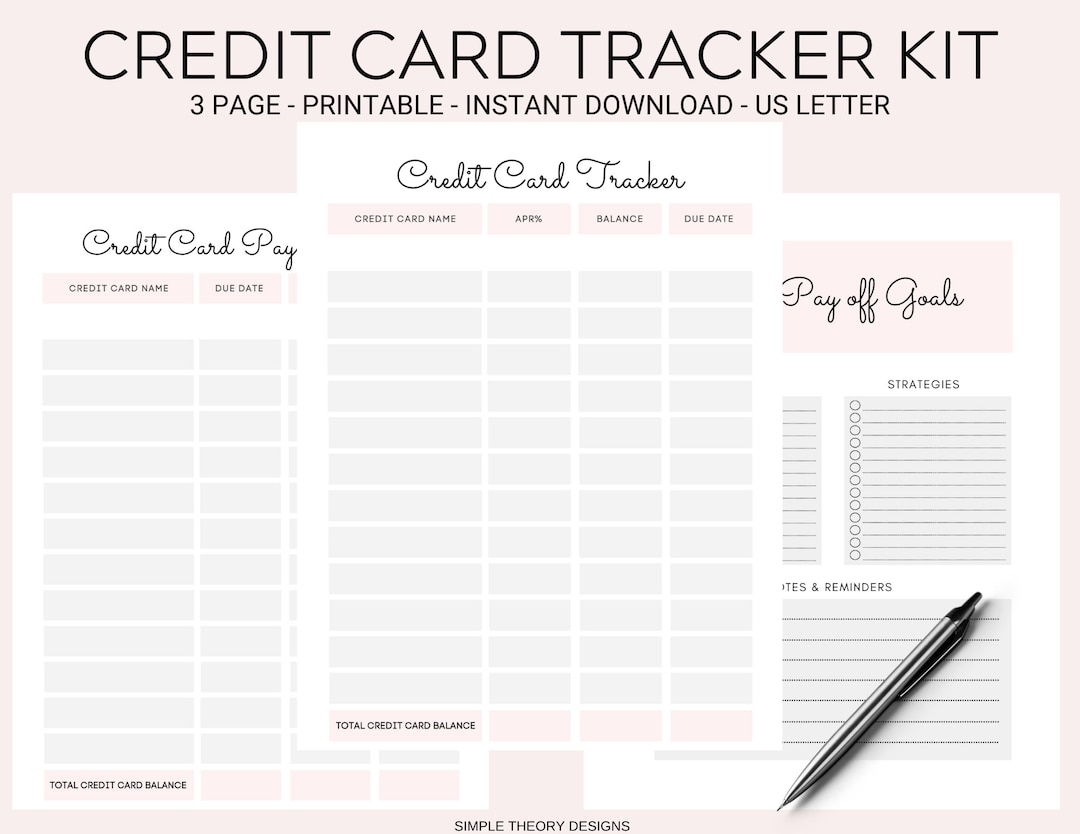
In today's digital age, online shopping has become a norm, and credit card transactions have increased significantly. However, with the rise of online transactions, there's a growing concern about the security and integrity of credit card data. In this article, we'll delve into the world of online credit card users tracking protocol, exploring how websites track users, and what measures can be taken to ensure secure credit card transactions.How Websites Track Users
Websites use various techniques to track users, including: *- Cookies: Websites use cookies to store information about users' browsing history, preferences, and behavior.
- Tracking pixels: Tracking pixels are small images embedded in web pages that help websites track user interactions.
- Device fingerprinting: Websites can collect information about users' device configuration, such as operating system, browser, and version.
- IP address tracking: Websites can track users' IP addresses to determine their location and browsing behavior.

Cardholder Verification Value (CVV)
One essential component of the online credit card users tracking protocol is the Cardholder Verification Value (CVV). The CVV is a three-digit code located on the back of a credit card, and it's used to verify the cardholder's identity. When a user makes an online purchase, the CVV is required to complete the transaction.Card Verification Value (CVV2)
Another critical component of the online credit card users tracking protocol is the Card Verification Value (CVV2). The CVV2 is a three-digit code located on the front of a credit card, and it's used to verify the card's authenticity.Encryption and Tokenization