### Google Wi-Fi Setup for Extortion Types: Understanding the Risks and Safeguards ###
Why Wi-Fi Networks Are Vulnerable to Hacks
Wireless networks are increasingly becoming a common target for various types of attacks, including but not limited to MITM (Man-in-the-middle) attacks, brute-force attacks, and phishing. These attacks not only disrupt services but also result in stolen data, posing a significant concern for both personal and business users. To mitigate these risks, encryption methods, VPNs (Virtual Private Networks), and digital certificates play a crucial role in securing Wi-Fi networks. ### ####Global Use and Need for Secure Setup
The COVID-19 pandemic accelerated the global use of Wi-Fi networks for remote work, education, and communication. With the convenience of staying connected comes a heightened risk of hacking and data breaches. Ensuring a strong password, including a mix of letters, numbers, and special characters, significantly reduces the risk of unauthorized access. However, using a combination of methods such as WPA3 and implementing robust network segmentation through a solution like the SecureW2 Join Now PKI and Cloud RADIUS offers an additional layer of security, protecting Wi-Fi networks from potential intrusions like those involved in extortion methods. ### ####The Ongoing Threat

Easy Steps to Enhance Wi-Fi Security
- Password Protection: Ensure you're using a strong and unique password for each network. - Network Segmentations: Implement robust network segmentation to limit potential intrusions. - Two-Factor Authentication: Add an extra layer of security with two-factor authentication (2FA) methods. - Regular Updates: Regularly update your Wi-Fi router and network settings to address any known vulnerabilities. - Monitoring: Continuously monitor your network for any unusual activity. ###Setting Up Your Google Wi-Fi
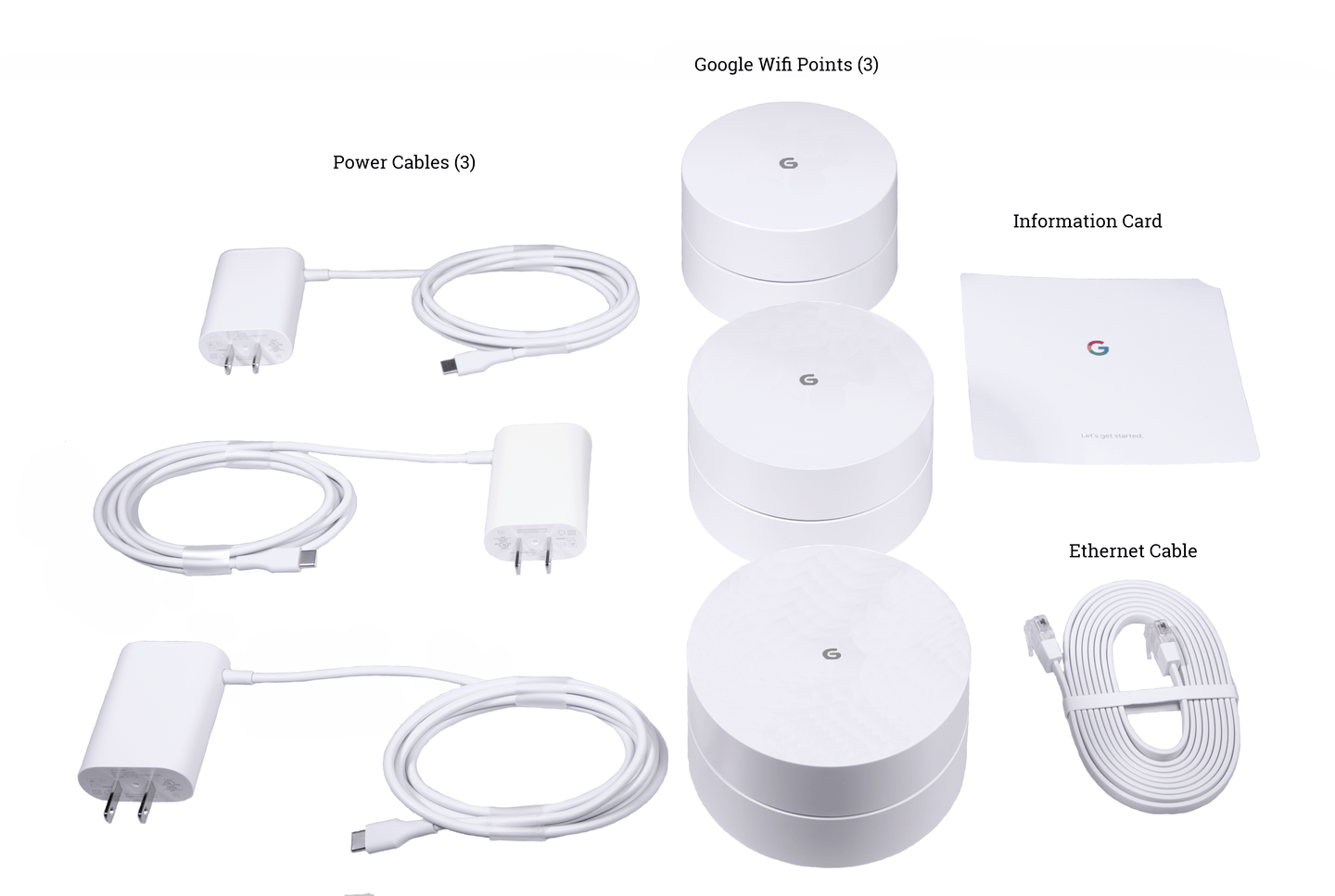
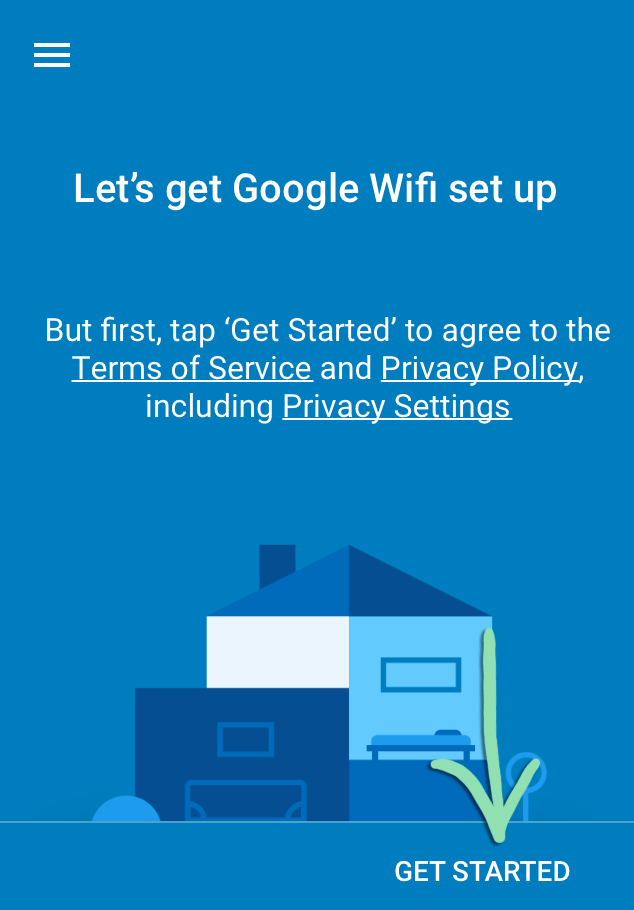
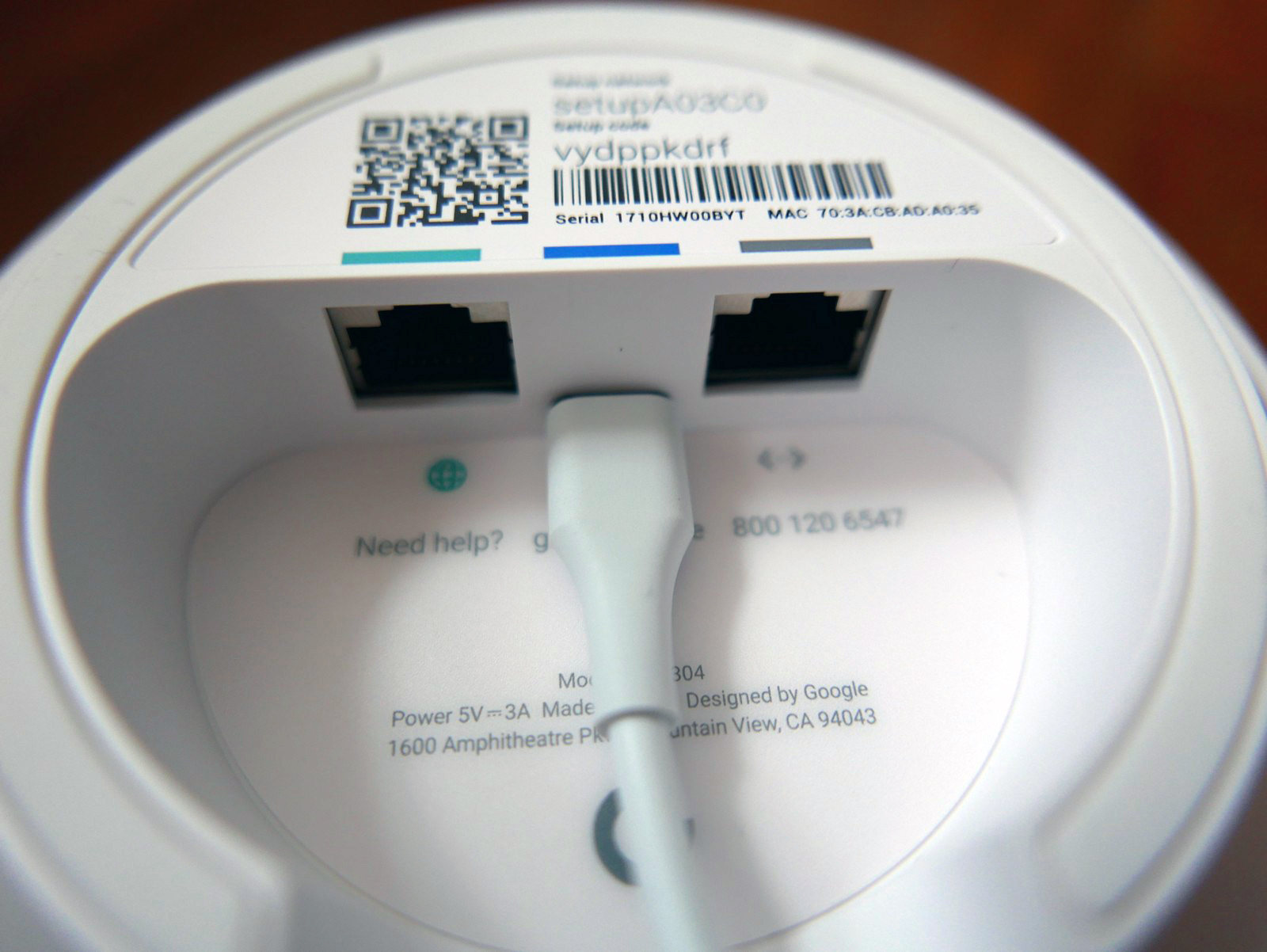
- **Step 1:** Connect your router to the power source. - **Step 2:** Use the Google Home app to setup your Wi-Fi router. Ensure the device is connected to your smartphone via Bluetooth. ###Special Cases and Considerations

As we can see from the illustration, Google Wi-Fi Setup For Extortion Types has many fascinating aspects to explore.
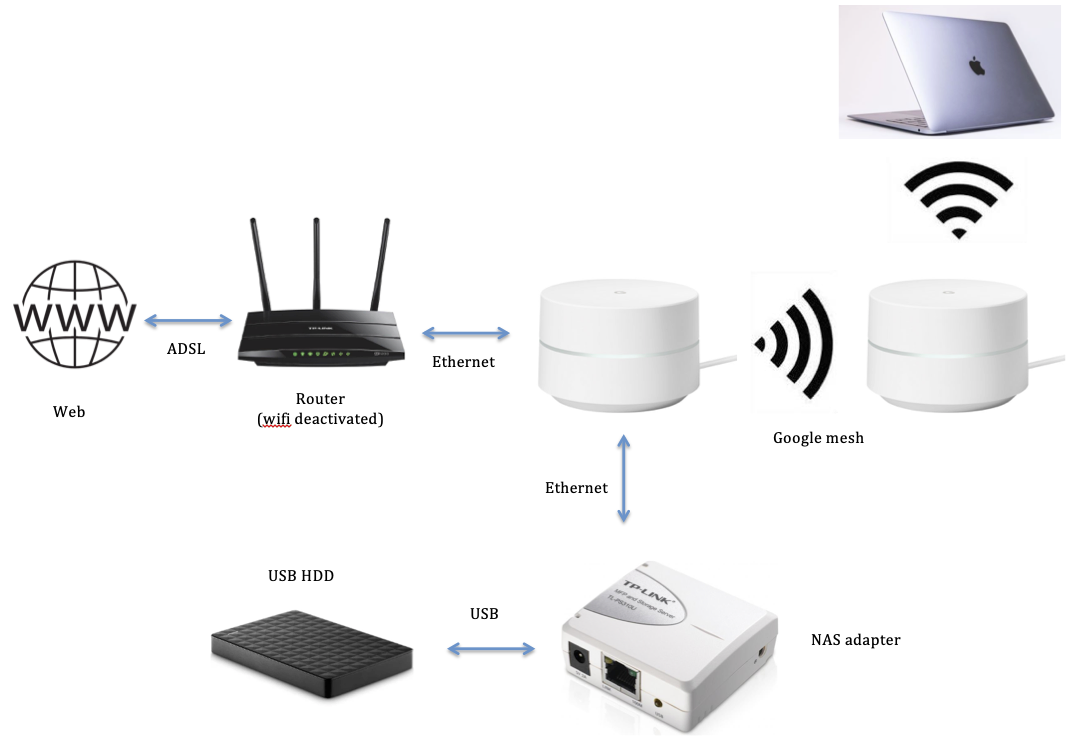
- Mesh Networks: For widespread coverage, mesh networks like Google Wi-Fi can be set up by connecting additional units to the main router. Each unit can expand the coverage area, creating a network of locations that offer stable and consistent speeds. ###