How to Protect Your Identity: Essential Tips and Strategies
Protecting your identity is a crucial aspect of maintaining your personal and financial security. With the increasing number of cyber threats and identity theft cases, it's essential to take proactive steps to safeguard your sensitive information. In this article, we'll explore some essential tips and strategies on how to protect your identity, including being defensive with sensitive information, using password managers, enabling two-factor authentication, and checking credit reports.
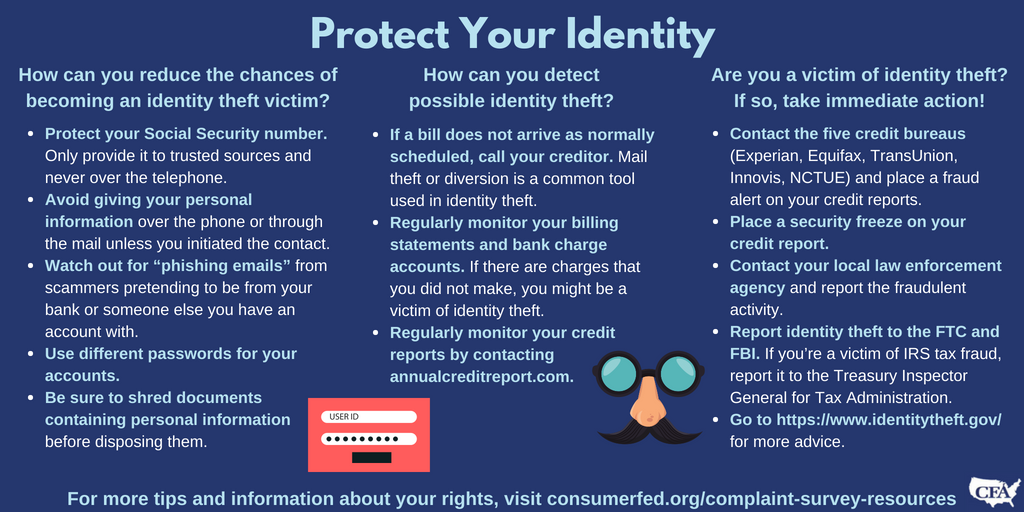
Understanding Identity Theft
Identity theft is a serious crime where an individual's personal and financial information is stolen and used for malicious purposes. It can take months or even years to discover that you're a victim of identity theft, and recovering from it can be a lengthy and costly process. Therefore, prevention is key to protecting your identity.
Be Defensive with Sensitive Information
Be cautious when sharing sensitive information over the internet, such as social media platforms, email, or text messages. These methods may not be secure, and cybercriminals can easily intercept and steal your information. It's essential to be defensive with sensitive information by using secure channels, such as encrypted messaging apps or secured email services.

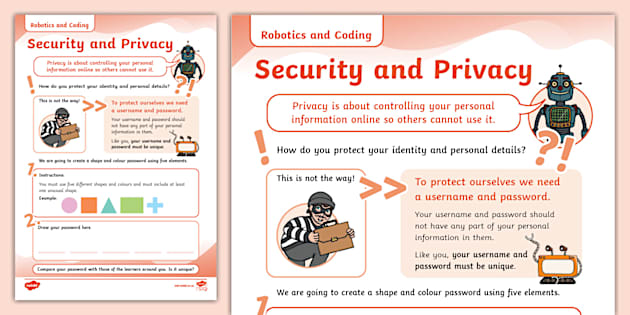
Use Password Managers
Using password managers can help you generate and store unique, complex passwords for each of your online accounts. This can help prevent hackers from accessing your sensitive information. Some popular password managers include LastPass, 1Password, and Dashlane. When choosing a password manager, look for features such as encryption, two-factor authentication, and password generation.
Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security to your online accounts by requiring you to provide a second form of verification, such as a fingerprint or a one-time password, in addition to your password. This can help prevent hackers from accessing your sensitive information even if they have your password. When enabling two-factor authentication, look for services that use secure authentication methods, such as token-based or SMS-based verification.
Check Credit Reports

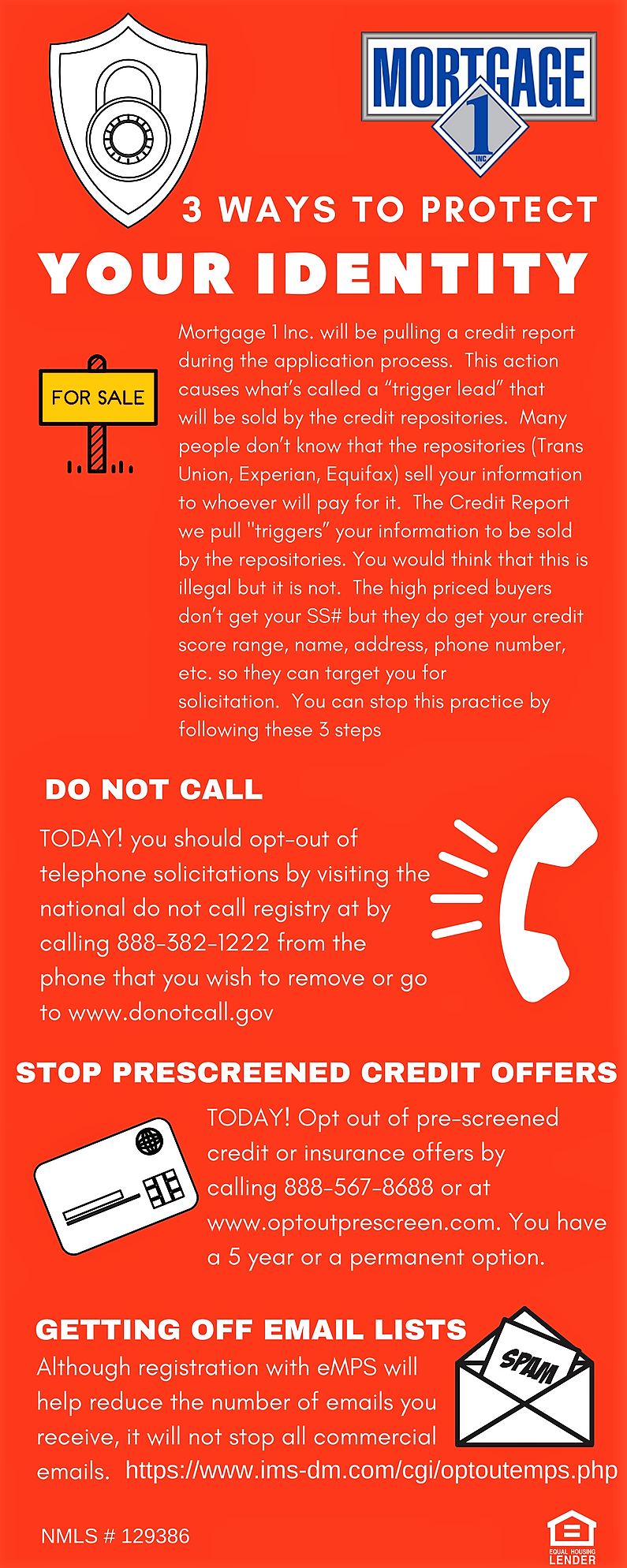
Checking your credit reports regularly can help you detect any suspicious activity, such as new accounts or credit inquiries, that may indicate identity theft. You can request a free credit report from each of the three major credit bureaus, Experian, Equifax, and TransUnion, once a year. When reviewing your credit report, look for discrepancies, such as accounts you didn't open, and contact the credit bureau to report any errors.
Reporting and Recovering from Identity Theft
If you suspect that you're a victim of identity theft, report it to the relevant authorities, such as the Federal Trade Commission (FTC) or your local police department, immediately. The FTC provides resources and tips on how to report and recover from identity theft, including creating an identity theft report and checking your credit reports.
Conclusion
Protecting your identity is a crucial aspect of maintaining your personal and financial security. By being defensive with sensitive information, using password managers, enabling two-factor authentication, and checking credit reports, you can significantly reduce the risk of identity theft. Remember to report and recover from identity theft if you suspect that you're a victim. Stay informed and take proactive steps to protect your identity and prevent cyber threats.

Additional Tips
- Shred sensitive documents, such as old credit card statements or bank statements.
- Monitor your bank and credit card statements regularly for suspicious activity.
- Use a credit freeze to prevent new accounts from being opened in your name.
- Consider using an identity theft protection service, such as LifeLock or IdentityForce, to monitor your credit reports and alert you to any suspicious activity.
Key Takeaways
Protecting your identity is a critical aspect of maintaining your personal and financial security.
Report and recover from identity theft if you suspect that you're a victim, and take proactive steps to protect your identity and prevent cyber threats.